Dependency Scanning
Offering: GitLab.com, Self-managed, GitLab Dedicated
Dependency Scanning analyzes your application’s dependencies for known vulnerabilities. All dependencies are scanned, including transitive dependencies, also known as nested dependencies.
Dependency Scanning is often considered part of Software Composition Analysis (SCA). SCA can contain aspects of inspecting the items your code uses. These items typically include application and system dependencies that are almost always imported from external sources, rather than sourced from items you wrote yourself.
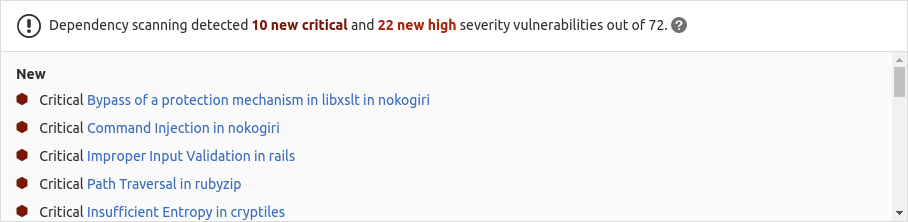
Dependency Scanning can run in the development phase of your application’s life cycle. Every time a pipeline runs, vulnerabilities are identified and compared between the source and target branches. Vulnerabilities and their severity are listed in the merge request, enabling you to proactively address the risk to your application, before the code change is committed. Vulnerabilities can also be identified outside a pipeline by Continuous Vulnerability Scanning.
GitLab offers both Dependency Scanning and Container Scanning to ensure coverage for all of these dependency types. To cover as much of your risk area as possible, we encourage you to use all of our security scanners. For a comparison of these features, see Dependency Scanning compared to Container Scanning.
- For an overview, see Dependency Scanning
- For an interactive reading and how-to demo of this Dependency Scanning documentation, see How to use dependency scanning tutorial hands-on GitLab Application Security part 3
- For other interactive reading and how-to demos, see Get Started With GitLab Application Security Playlist
Supported languages and package managers
The following languages and dependency managers are supported:
| Language | Language versions | Package manager | Supported files | Processes multiple files? |
|---|---|---|---|---|
| .NET | All versions | NuGet | packages.lock.json
| Y |
| C# | ||||
| C | All versions | Conan | conan.lock
| Y |
| C++ | ||||
| Go | All versions | Go |
| Y |
| Java and Kotlin (not Android)1 | 8 LTS, 11 LTS, 17 LTS, or 21 LTS2 | Gradle3 |
| N |
| Maven8 | pom.xml
| N | ||
| JavaScript and TypeScript | All versions | npm |
| Y |
| yarn | yarn.lock
| Y | ||
| pnpm4 | pnpm-lock.yaml
| Y | ||
| PHP | All versions | Composer | composer.lock
| Y |
| Python | 3.99, 3.105 | setuptools | setup.py
| N |
| pip |
| N | ||
| Pipenv | N | |||
| Poetry6 | poetry.lock
| N | ||
| Ruby | All versions | Bundler |
| Y |
| Scala | All versions | sbt7 | build.sbt
| N |
-
Support for Kotlin projects for Android is tracked in issue 336866.
-
Java 21 LTS for sbt is limited to version 1.9.7. Support for more sbt versions can be tracked in issue 430335. It is not supported when FIPS mode is enabled.
-
Gradle is not supported when FIPS mode is enabled.
-
Support for
pnpmlockfiles was introduced in GitLab 15.11.pnpmlockfiles do not store bundled dependencies, so the reported dependencies may differ fromnpmoryarn. -
For support of
Python 3.10, add the following stanza to the GitLab CI/CD configuration file. This specifies that thePython 3.10image is to be used, instead of the defaultPython 3.9.gemnasium-dependency_scanning: image: name: $CI_TEMPLATE_REGISTRY_HOST/security-products/gemnasium-python:4-python-3.10 -
Support for Poetry projects with a
poetry.lockfile was added in GitLab 15.0. Support for projects without apoetry.lockfile is tracked in issue: Poetry's pyproject.toml support for dependency scanning. -
Support for sbt 1.0.x was deprecated in GitLab 16.8.
-
Support for Maven below 3.8.8 was deprecated in GitLab 16.9 and will be removed in GitLab 17.0.
-
Support for Python 3.9 was deprecated in GitLab 16.9 and will be removed in GitLab 17.0.
Dependency detection
Dependency Scanning automatically detects the languages used in the repository. All analyzers
matching the detected languages are run. There is usually no need to customize the selection of
analyzers. We recommend not specifying the analyzers so you automatically use the full selection for
best coverage, avoiding the need to make adjustments when there are deprecations or removals.
However, you can override the selection using the variable DS_EXCLUDED_ANALYZERS.
The language detection relies on CI job rules and searches a
maximum of two directory levels from the repository’s root. For example, the
gemnasium-dependency_scanning job is enabled if a repository contains either Gemfile,
api/Gemfile, or api/client/Gemfile, but not if the only supported dependency file is
api/v1/client/Gemfile.
For Java and Python, when a supported dependency file is detected, Dependency Scanning attempts to build the project and execute some Java or Python commands to get the list of dependencies. For all other projects, the lock file is parsed to obtain the list of dependencies without needing to build the project first.
When a supported dependency file is detected, all dependencies, including transitive dependencies are analyzed. There is no limit to the depth of nested or transitive dependencies that are analyzed.
Analyzers
Dependency Scanning supports the following official Gemnasium-based analyzers:
gemnasiumgemnasium-mavengemnasium-python
The analyzers are published as Docker images, which Dependency Scanning uses to launch dedicated containers for each analysis. You can also integrate a custom security scanner.
Each analyzer is updated as new versions of Gemnasium are released. For more information, see the analyzer Release Process documentation.
How analyzers obtain dependency information
GitLab analyzers obtain dependency information using one of the following two methods:
- Parsing lockfiles directly.
- Running a package manager or build tool to generate a dependency information file which is then parsed.
Obtaining dependency information by parsing lockfiles
The following package managers use lockfiles that GitLab analyzers are capable of parsing directly:
| Package Manager | Supported File Format Versions | Tested Package Manager Versions |
|---|---|---|
| Bundler | Not applicable | 1.17.3, 2.1.4 |
| Composer | Not applicable | 1.x |
| Conan | 0.4 | 1.x |
| Go | Not applicable | 1.x1 |
| NuGet | v1, v22 | 4.9 |
| npm | v1, v2, v33 | 6.x, 7.x, 9.x |
| pnpm | v5, v6 | 7.x, 8.x |
| yarn | v1, v24, v34 | 1.x, 2.x, 3.x |
| Poetry | v1 | 1.x |
-
Dependency Scanning only parses
go.sumif it's unable to generate the build list used by the Go project. -
Support for NuGet version 2 lock files was introduced in GitLab 16.2.
-
Support for
lockfileVersion = 3was introduced in GitLab 15.7. -
Support for Yarn
v2andv3was introduced in GitLab 15.11. However, this feature is also available to versions of GitLab 15.0 and later.The following features are not supported for Yarn
v2orv3:Yarn files that contain a patch, a workspace, or both, are still processed, but these features are ignored.
Obtaining dependency information by running a package manager to generate a parsable file
To support the following package managers, the GitLab analyzers proceed in two steps:
- Execute the package manager or a specific task, to export the dependency information.
- Parse the exported dependency information.
| Package Manager | Pre-installed Versions | Tested Versions |
|---|---|---|
| sbt | 1.6.2 | 1.0.4, 1.1.6, 1.2.8, 1.3.12, 1.4.6, 1.5.8, 1.6.2 1.7.3 1.8.3 1.9.6 1.9.7 |
| maven | 3.6.3 | 3.6.31 |
| Gradle | 6.7.12, 7.3.32 | 5.6.4, 6.7, 6.9, 7.3 8.4 |
| setuptools | 58.1.0 | >= 65.6.3 |
| pip | 22.0.4 | 20.x |
| Pipenv | 2022.1.8 | 2022.1.83, 2022.1.8 |
| Go | 1.18 | 1.184 |
-
This test uses the default version of
mavenspecified by the.tool-versionsfile. -
Different versions of Java require different versions of Gradle. The versions of Gradle listed in the above table are pre-installed in the analyzer image. The version of Gradle used by the analyzer depends on whether your project uses a
gradlew(Gradle wrapper) file or not:-
If your project does not use a
gradlewfile, then the analyzer automatically switches to one of the pre-installed Gradle versions, based on the version of Java specified by theDS_JAVA_VERSIONvariable. By default, the analyzer uses Java 17 and Gradle 7.3.3.For Java versions
8and11, Gradle6.7.1is automatically selected, and for Java version17, Gradle7.3.3is automatically selected. -
If your project does use a
gradlewfile, then the version of Gradle pre-installed in the analyzer image is ignored, and the version specified in yourgradlewfile is used instead.
-
-
This test confirms that if a
Pipfile.lockfile is found, it is used by Gemnasium to scan the exact package versions listed in this file. -
Because of the implementation of
go build, the Go build process requires network access, a pre-loaded mod cache viago mod download, or vendored dependencies. For more information, refer to the Go documentation on compiling packages and dependencies.
How analyzers are triggered
GitLab relies on rules:exists to start the relevant analyzers for the languages detected by the presence of the
Supported files in the repository as shown in the table above.
The current detection logic limits the maximum search depth to two levels. For example, the gemnasium-dependency_scanning job is enabled if
a repository contains either a Gemfile.lock, api/Gemfile.lock, or api/client/Gemfile.lock, but not if the only supported dependency file is api/v1/client/Gemfile.lock.
When a supported dependency file is detected, all dependencies, including transitive dependencies are analyzed. There is no limit to the depth of nested or transitive dependencies that are analyzed.
How multiple files are processed
Python
We only execute one installation in the directory where either a requirements file or a lock file has been detected. Dependencies are only analyzed by gemnasium-python for the first file that is detected. Files are searched for in the following order:
-
requirements.txt,requirements.pip, orrequires.txtfor projects using Pip. -
PipfileorPipfile.lockfor projects using Pipenv. -
poetry.lockfor projects using Poetry. -
setup.pyfor project using Setuptools.
The search begins with the root directory and then continues with subdirectories if no builds are found in the root directory. Consequently a Poetry lock file in the root directory would be detected before a Pipenv file in a subdirectory.
Java and Scala
We only execute one build in the directory where a build file has been detected. For large projects that include
multiple Gradle, Maven, or sbt builds, or any combination of these, gemnasium-maven only analyzes dependencies for the first build file
that is detected. Build files are searched for in the following order:
-
pom.xmlfor single or multi-module Maven projects. -
build.gradleorbuild.gradle.ktsfor single or multi-project Gradle builds. -
build.sbtfor single or multi-project sbt builds.
The search begins with the root directory and then continues with subdirectories if no builds are found in the root directory. Consequently an sbt build file in the root directory would be detected before a Gradle build file in a subdirectory.
JavaScript
The following analyzers are executed, each of which have different behavior when processing multiple files:
-
Supports multiple lockfiles
-
Does not support multiple lockfiles. When multiple lockfiles exist,
Retire.jsanalyzes the first lockfile discovered while traversing the directory tree in alphabetical order.
From GitLab 14.8 the gemnasium analyzer scans supported JavaScript projects for vendored libraries
(that is, those checked into the project but not managed by the package manager).
Go
Multiple files are supported. When a go.mod file is detected, the analyzer attempts to generate a build list using
Minimal Version Selection. If a non-fatal error is encountered, the analyzer falls back to parsing the
available go.sum file. The process is repeated for every detected go.mod and go.sum file.
PHP, C, C++, .NET, C#, Ruby, JavaScript
The analyzer for these languages supports multiple lockfiles.
Support for additional languages
Support for additional languages, dependency managers, and dependency files are tracked in the following issues:
| Package Managers | Languages | Supported files | Scan tools | Issue |
|---|---|---|---|---|
| Poetry | Python | pyproject.toml
| Gemnasium | GitLab#32774 |
Configuration
Enable the dependency scanning analyzer to ensure it scans your application’s dependencies for known vulnerabilities. You can then adjust its behavior by using CI/CD variables.
Enabling the analyzer
Prerequisites:
- The
teststage is required in the.gitlab-ci.ymlfile. - With self-managed runners you need a GitLab Runner with the
dockerorkubernetesexecutor. - If you’re using SaaS runners on GitLab.com, this is enabled by default.
To enable the analyzer, either:
- Enable Auto DevOps, which includes dependency scanning.
- Edit the
.gitlab-ci.ymlfile manually. Use this method if your.gitlab-ci.ymlfile is complex. - Use a preconfigured merge request.
- Create a scan execution policy that enforces dependency scanning.
Edit the .gitlab-ci.yml file manually
This method requires you to manually edit the existing .gitlab-ci.yml file. Use this method if
your GitLab CI/CD configuration file is complex.
To enable dependency scanning:
- On the left sidebar, select Search or go to and find your project.
- Select Build > Pipeline editor.
- If no
.gitlab-ci.ymlfile exists, select Configure pipeline, then delete the example content. -
Copy and paste the following to the bottom of the
.gitlab-ci.ymlfile. If anincludeline already exists, add only thetemplateline below it.include: - template: Jobs/Dependency-Scanning.gitlab-ci.yml -
Select the Validate tab, then select Validate pipeline.
The message Simulation completed successfully confirms the file is valid.
- Select the Edit tab.
- Complete the fields. Do not use the default branch for the Branch field.
- Select the Start a new merge request with these changes checkbox, then select Commit changes.
- Complete the fields according to your standard workflow, then select Create merge request.
- Review and edit the merge request according to your standard workflow, then select Merge.
Pipelines now include a dependency scanning job.
Use a preconfigured merge request
-
Introduced in GitLab 14.1 with a flag named
sec_dependency_scanning_ui_enable. Enabled by default. -
Generally available in GitLab 14.2. Feature flag
sec_dependency_scanning_ui_enableremoved.
This method automatically prepares a merge request that includes the dependency scanning template
in the .gitlab-ci.yml file. You then merge the merge request to enable dependency scanning.
.gitlab-ci.yml file, or with a minimal configuration
file. If you have a complex GitLab configuration file it might not be parsed successfully, and an
error might occur. In that case, use the manual method instead.To enable dependency scanning:
- On the left sidebar, select Search or go to and find your project.
- Select Secure > Security configuration.
- In the Dependency Scanning row, select Configure with a merge request.
- Select Create merge request.
- Review the merge request, then select Merge.
Pipelines now include a dependency scanning job.
Running jobs in merge request pipelines
See Use security scanning tools with merge request pipelines
Customizing analyzer behavior
You can use CI/CD variables to customize dependency scanning behavior.
Overriding dependency scanning jobs
To override a job definition (for example, to change properties like variables or dependencies),
declare a new job with the same name as the one to override. Place this new job after the template
inclusion and specify any additional keys under it. For example, this disables DS_REMEDIATE for
the gemnasium analyzer:
include:
- template: Jobs/Dependency-Scanning.gitlab-ci.yml
gemnasium-dependency_scanning:
variables:
DS_REMEDIATE: "false"
To override the dependencies: [] attribute, add an override job as above, targeting this attribute:
include:
- template: Jobs/Dependency-Scanning.gitlab-ci.yml
gemnasium-dependency_scanning:
dependencies: ["build"]
Available CI/CD variables
You can use CI/CD variables to customize dependency scanning behavior.
Global analyzer settings
The following variables allow configuration of global dependency scanning settings.
| CI/CD variables | Description |
|---|---|
ADDITIONAL_CA_CERT_BUNDLE
| Bundle of CA certificates to trust. The bundle of certificates provided here is also used by other tools during the scanning process, such as git, yarn, or npm. For more details, see Custom TLS certificate authority.
|
DS_EXCLUDED_ANALYZERS
| Specify the analyzers (by name) to exclude from Dependency Scanning. For more information, see Analyzers. |
DS_EXCLUDED_PATHS
| Exclude files and directories from the scan based on the paths. A comma-separated list of patterns. Patterns can be globs (see doublestar.Match for supported patterns), or file or folder paths (for example, doc,spec). Parent directories also match patterns. Default: "spec, test, tests, tmp".
|
DS_IMAGE_SUFFIX
| Suffix added to the image name. (GitLab team members can view more information in this confidential issue: https://gitlab.com/gitlab-org/gitlab/-/issues/354796). Automatically set to "-fips" when FIPS mode is enabled.
|
DS_MAX_DEPTH
| Defines how many directory levels deep that the analyzer should search for supported files to scan. A value of -1 scans all directories regardless of depth. Default: 2.
|
SECURE_ANALYZERS_PREFIX
| Override the name of the Docker registry providing the official default images (proxy). |
Analyzer-specific settings
The following variables configure the behavior of specific dependency scanning analyzers.
| CI/CD variable | Analyzer | Default | Description |
|---|---|---|---|
GEMNASIUM_DB_LOCAL_PATH
| gemnasium
| /gemnasium-db
| Path to local Gemnasium database. |
GEMNASIUM_DB_UPDATE_DISABLED
| gemnasium
| "false"
| Disable automatic updates for the gemnasium-db advisory database. For usage see Hosting a copy of the Gemnasium advisory database.
|
GEMNASIUM_DB_REMOTE_URL
| gemnasium
| https://gitlab.com/gitlab-org/security-products/gemnasium-db.git
| Repository URL for fetching the Gemnasium database. |
GEMNASIUM_DB_REF_NAME
| gemnasium
| master
| Branch name for remote repository database. GEMNASIUM_DB_REMOTE_URL is required.
|
DS_REMEDIATE
| gemnasium
|
"true", "false" in FIPS mode
| Enable automatic remediation of vulnerable dependencies. Not supported in FIPS mode. |
DS_REMEDIATE_TIMEOUT
| gemnasium
| 5m
| Timeout for auto-remediation. |
GEMNASIUM_LIBRARY_SCAN_ENABLED
| gemnasium
| "true"
| Enable detecting vulnerabilities in vendored JavaScript libraries (libraries which are not managed by a package manager). This functionality requires a JavaScript lockfile to be present in a commit, otherwise Dependency Scanning is not executed and vendored files are not scanned. Dependency scanning uses the Retire.js scanner to detect a limited set of vulnerabilities. For details of which vulnerabilities are detected, see the Retire.js repository. Introduced in GitLab 14.8. |
DS_INCLUDE_DEV_DEPENDENCIES
| gemnasium
| "true"
| When set to "false", development dependencies and their vulnerabilities are not reported. Only projects using Composer, npm, pnpm, Pipenv or Poetry are supported. Introduced in GitLab 15.1.
|
GOOS
| gemnasium
| "linux"
| The operating system for which to compile Go code. |
GOARCH
| gemnasium
| "amd64"
| The architecture of the processor for which to compile Go code. |
GOFLAGS
| gemnasium
| The flags passed to the go build tool.
| |
GOPRIVATE
| gemnasium
| A list of glob patterns and prefixes to be fetched from source. For more information, see the Go private modules documentation. | |
DS_JAVA_VERSION
| gemnasium-maven
| 17
| Version of Java. Available versions: 8, 11, 17, 21.
|
MAVEN_CLI_OPTS
| gemnasium-maven
| "-DskipTests --batch-mode"
| List of command line arguments that are passed to maven by the analyzer. See an example for using private repositories.
|
GRADLE_CLI_OPTS
| gemnasium-maven
| List of command line arguments that are passed to gradle by the analyzer.
| |
SBT_CLI_OPTS
| gemnasium-maven
| List of command-line arguments that the analyzer passes to sbt.
| |
PIP_INDEX_URL
| gemnasium-python
| https://pypi.org/simple
| Base URL of Python Package Index. |
PIP_EXTRA_INDEX_URL
| gemnasium-python
| Array of extra URLs of package indexes to use in addition to PIP_INDEX_URL. Comma-separated. Warning: Read the following security consideration when using this environment variable.
| |
PIP_REQUIREMENTS_FILE
| gemnasium-python
| Pip requirements file to be scanned. This is a filename and not a path. When this environment variable is set only the specified file is scanned. | |
PIPENV_PYPI_MIRROR
| gemnasium-python
| If set, overrides the PyPi index used by Pipenv with a mirror. | |
DS_PIP_VERSION
| gemnasium-python
| Force the install of a specific pip version (example: "19.3"), otherwise the pip installed in the Docker image is used.
| |
DS_PIP_DEPENDENCY_PATH
| gemnasium-python
| Path to load Python pip dependencies from. |
Other variables
The previous tables are not an exhaustive list of all variables that can be used. They contain all specific GitLab and analyzer variables we support and test. There are many variables, such as environment variables, that you can pass in and they do work. This is a large list, many of which we may be unaware of, and as such is not documented.
For example, to pass the non-GitLab environment variable HTTPS_PROXY to all Dependency Scanning jobs,
set it as a CI/CD variable in your .gitlab-ci.yml
file like this:
variables:
HTTPS_PROXY: "https://squid-proxy:3128"
Alternatively we may use it in specific jobs, like Dependency Scanning:
dependency_scanning:
variables:
HTTPS_PROXY: $HTTPS_PROXY
As we have not tested all variables you may find some do work and others do not. If one does not work and you need it we suggest submitting a feature request or contributing to the code to enable it to be used.
Custom TLS certificate authority
Dependency Scanning allows for use of custom TLS certificates for SSL/TLS connections instead of the default shipped with the analyzer container image.
Support for custom certificate authorities was introduced in the following versions.
| Analyzer | Version |
|---|---|
gemnasium
| v2.8.0 |
gemnasium-maven
| v2.9.0 |
gemnasium-python
| v2.7.0 |
Using a custom TLS certificate authority
To use a custom TLS certificate authority, assign the
text representation of the X.509 PEM public-key certificate
to the CI/CD variable ADDITIONAL_CA_CERT_BUNDLE.
For example, to configure the certificate in the .gitlab-ci.yml file:
variables:
ADDITIONAL_CA_CERT_BUNDLE: |
-----BEGIN CERTIFICATE-----
MIIGqTCCBJGgAwIBAgIQI7AVxxVwg2kch4d56XNdDjANBgkqhkiG9w0BAQsFADCB
...
jWgmPqF3vUbZE0EyScetPJquRFRKIesyJuBFMAs=
-----END CERTIFICATE-----
Using private Maven repositories
If your private Maven repository requires login credentials,
you can use the MAVEN_CLI_OPTS CI/CD variable.
Read more on how to use private Maven repositories.
FIPS-enabled images
- Introduced in GitLab 14.10. GitLab team members can view more information in this confidential issue:
https://gitlab.com/gitlab-org/gitlab/-/issues/354796 - Introduced in GitLab 15.0 - Gemnasium uses FIPS-enabled images when FIPS mode is enabled.
GitLab also offers FIPS-enabled Red Hat UBI
versions of the Gemnasium images. When FIPS mode is enabled in the GitLab instance, Gemnasium
scanning jobs automatically use the FIPS-enabled images. To manually switch to FIPS-enabled images,
set the variable DS_IMAGE_SUFFIX to "-fips".
Dependency scanning for Gradle projects and auto-remediation for Yarn projects are not supported in FIPS mode.
Output
Dependency Scanning produces the following output:
- Dependency scanning report: Contains details of all vulnerabilities detected in dependencies.
- CycloneDX Software Bill of Materials: Software Bill of Materials (SBOM) for each supported lock or build file detected.
Dependency scanning report
Dependency scanning outputs a report containing details of all vulnerabilities. The report is
processed internally and the results are shown in the UI. The report is also output as an artifact
of the dependency scanning job, named gl-dependency-scanning-report.json.
For more details of the dependency scanning report, see:
CycloneDX Software Bill of Materials
- Introduced in GitLab 14.8 in Beta.
- Generally available in GitLab 15.7.
Dependency Scanning outputs a CycloneDX Software Bill of Materials (SBOM) for each supported lock or build file it detects.
The CycloneDX SBOMs are:
- Named
gl-sbom-<package-type>-<package-manager>.cdx.json. - Available as job artifacts of the dependency scanning job.
- Saved in the same directory as the detected lock or build files.
For example, if your project has the following structure:
.
├── ruby-project/
│ └── Gemfile.lock
├── ruby-project-2/
│ └── Gemfile.lock
├── php-project/
│ └── composer.lock
└── go-project/
└── go.sum
Then the Gemnasium scanner generates the following CycloneDX SBOMs:
.
├── ruby-project/
│ ├── Gemfile.lock
│ └── gl-sbom-gem-bundler.cdx.json
├── ruby-project-2/
│ ├── Gemfile.lock
│ └── gl-sbom-gem-bundler.cdx.json
├── php-project/
│ ├── composer.lock
│ └── gl-sbom-packagist-composer.cdx.json
└── go-project/
├── go.sum
└── gl-sbom-go-go.cdx.json
Merging multiple CycloneDX SBOMs
You can use a CI/CD job to merge the multiple CycloneDX SBOMs into a single SBOM. GitLab uses CycloneDX Properties to store implementation-specific details in the metadata of each CycloneDX SBOM, such as the location of build and lock files. If multiple CycloneDX SBOMs are merged together, this information is removed from the resulting merged file.
For example, the following .gitlab-ci.yml extract demonstrates how the Cyclone SBOM files can be
merged, and the resulting file validated.
stages:
- test
- merge-cyclonedx-sboms
include:
- template: Jobs/Dependency-Scanning.gitlab-ci.yml
merge cyclonedx sboms:
stage: merge-cyclonedx-sboms
image:
name: cyclonedx/cyclonedx-cli:0.24.2
entrypoint: [""]
script:
- apt-get update && apt-get install -y jq
- find . -name "gl-sbom-*.cdx.json" -exec cyclonedx merge --output-file gl-sbom-all.cdx.json --input-files "{}" +
# remove duplicates from merged file. See https://github.com/CycloneDX/cyclonedx-cli/issues/188 for details.
- |
jq '. |
{
"bomFormat": .bomFormat,
"specVersion": .specVersion,
"serialNumber": .serialNumber,
"version": .version,
"metadata": {
"tools": [
(.metadata.tools | unique[])
]
},
"components": [
(.components | unique[])
]
}' "gl-sbom-all.cdx.json" > gl-sbom-all.cdx.json.tmp && mv gl-sbom-all.cdx.json.tmp gl-sbom-all.cdx.json
# optional: validate the merged sbom
- cyclonedx validate --input-version v1_4 --input-file gl-sbom-all.cdx.json
artifacts:
paths:
- gl-sbom-all.cdx.json
Contributing to the vulnerability database
To find a vulnerability, you can search the GitLab Advisory Database.
You can also submit new vulnerabilities.
Running dependency scanning in an offline environment
For self-managed GitLab instances in an environment with limited, restricted, or intermittent access to external resources through the internet, some adjustments are required for dependency scanning jobs to run successfully. For more information, see Offline environments.
Requirements for offline dependency scanning
Here are the requirements for using dependency scanning in an offline environment:
- GitLab Runner with the
dockerorkubernetesexecutor. - Docker container registry with locally available copies of dependency scanning analyzer images.
-
If you have a limited access environment you need to allow access, such as using a proxy, to the advisory database:
https://gitlab.com/gitlab-org/security-products/gemnasium-db.git. If you are unable to permit access tohttps://gitlab.com/gitlab-org/security-products/gemnasium-db.gityou must host an offline copy of thisgitrepository and set theGEMNASIUM_DB_REMOTE_URLCI/CD variable to the URL of this repository. For more information on configuration variables, see Customizing analyzer behavior.This advisory database is constantly being updated, so you must periodically sync your local copy with GitLab.
GitLab Runner has a default pull policy of always,
meaning the runner tries to pull Docker images from the GitLab container registry even if a local
copy is available. The GitLab Runner pull_policy can be set to if-not-present
in an offline environment if you prefer using only locally available Docker images. However, we
recommend keeping the pull policy setting to always if not in an offline environment, as this
enables the use of updated scanners in your CI/CD pipelines.
Make GitLab dependency scanning analyzer images available inside your Docker registry
For dependency scanning with all supported languages and frameworks,
import the following default dependency scanning analyzer images from registry.gitlab.com into
your local Docker container registry:
registry.gitlab.com/security-products/gemnasium:4
registry.gitlab.com/security-products/gemnasium-maven:4
registry.gitlab.com/security-products/gemnasium-python:4
The process for importing Docker images into a local offline Docker registry depends on your network security policy. Consult your IT staff to find an accepted and approved process by which external resources can be imported or temporarily accessed. These scanners are periodically updated with new definitions, and you may be able to make occasional updates on your own.
For details on saving and transporting Docker images as a file, see the Docker documentation on
docker save, docker load,
docker export, and docker import.
Set dependency scanning CI/CD job variables to use local dependency scanning analyzers
Add the following configuration to your .gitlab-ci.yml file. You must change the value of
SECURE_ANALYZERS_PREFIX to refer to your local Docker container registry. You must also change the
value of GEMNASIUM_DB_REMOTE_URL to the location of your offline Git copy of the
gemnasium-db advisory database:
include:
- template: Jobs/Dependency-Scanning.gitlab-ci.yml
variables:
SECURE_ANALYZERS_PREFIX: "docker-registry.example.com/analyzers"
GEMNASIUM_DB_REMOTE_URL: "gitlab.example.com/gemnasium-db.git"
See explanations of the previous variables in the configuration section.
Hosting a copy of the gemnasium_db advisory database
The gemnasium_db Git repository is
used by gemnasium, gemnasium-maven, and gemnasium-python as the source of vulnerability data.
This repository updates at scan time to fetch the latest advisories. However, due to a restricted
networking environment, running this update is sometimes not possible. In this case, a user can do
one of the following:
Host a copy of the advisory database
If gemnasium-db is not reachable
from within the environment, the user can host their own Git copy. Then the analyzer can be
instructed to update the database from the user’s copy by using GEMNASIUM_DB_REMOTE_URL:
variables:
GEMNASIUM_DB_REMOTE_URL: https://users-own-copy.example.com/gemnasium-db/.git
...
Use a local clone
If a hosted copy is not possible, then the user can clone gemnasium-db
or create an archive before the scan and point the analyzer to the directory (using:
GEMNASIUM_DB_LOCAL_PATH). Turn off the analyzer’s self-update mechanism (using:
GEMNASIUM_DB_UPDATE_DISABLED). In this example, the database directory is created in the
before_script, before the gemnasium analyzer’s scan job:
...
gemnasium-dependency_scanning:
variables:
GEMNASIUM_DB_LOCAL_PATH: ./gemnasium-db-local
GEMNASIUM_DB_UPDATE_DISABLED: "true"
before_script:
- mkdir $GEMNASIUM_DB_LOCAL_PATH
- tar -xzf gemnasium_db.tar.gz -C $GEMNASIUM_DB_LOCAL_PATH
Using a proxy with Gradle projects
The Gradle wrapper script does not read the HTTP(S)_PROXY environment variables. See this upstream issue.
To make the Gradle wrapper script use a proxy, you can specify the options using the GRADLE_CLI_OPTS CI/CD variable:
variables:
GRADLE_CLI_OPTS: "-Dhttps.proxyHost=squid-proxy -Dhttps.proxyPort=3128 -Dhttp.proxyHost=squid-proxy -Dhttp.proxyPort=3128 -Dhttp.nonProxyHosts=localhost"
Using a proxy with Maven projects
Maven does not read the HTTP(S)_PROXY environment variables.
To make the Maven dependency scanner use a proxy, you can specify the options using the MAVEN_CLI_OPTS CI/CD variable:
variables:
MAVEN_CLI_OPTS: "-DproxySet=true -Dhttps.proxyHost=squid-proxy -Dhttps.proxyPort=3128 -Dhttp.proxyHost=squid-proxy -Dhttp.proxyPort=3218"
Specific settings for languages and package managers
See the following sections for configuring specific languages and package managers.
Python (pip)
If you need to install Python packages before the analyzer runs, you should use pip install --user in the before_script of the scanning job. The --user flag causes project dependencies to be installed in the user directory. If you do not pass the --user option, packages are installed globally, and they are not scanned and don’t show up when listing project dependencies.
Python (setuptools)
If you need to install Python packages before the analyzer runs, you should use python setup.py install --user in the before_script of the scanning job. The --user flag causes project dependencies to be installed in the user directory. If you do not pass the --user option, packages are installed globally, and they are not scanned and don’t show up when listing project dependencies.
When using self-signed certificates for your private PyPi repository, no extra job configuration (aside
from the template .gitlab-ci.yml above) is needed. However, you must update your setup.py to
ensure that it can reach your private repository. Here is an example configuration:
-
Update
setup.pyto create adependency_linksattribute pointing at your private repository for each dependency in theinstall_requireslist:install_requires=['pyparsing>=2.0.3'], dependency_links=['https://pypi.example.com/simple/pyparsing'], -
Fetch the certificate from your repository URL and add it to the project:
printf "\n" | openssl s_client -connect pypi.example.com:443 -servername pypi.example.com | sed -ne '/-BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p' > internal.crt -
Point
setup.pyat the newly downloaded certificate:import setuptools.ssl_support setuptools.ssl_support.cert_paths = ['internal.crt']
Python (Pipenv)
If running in a limited network connectivity environment, you must configure the PIPENV_PYPI_MIRROR
variable to use a private PyPi mirror. This mirror must contain both default and development dependencies.
variables:
PIPENV_PYPI_MIRROR: https://pypi.example.com/simple
Alternatively, if it’s not possible to use a private registry, you can load the required packages
into the Pipenv virtual environment cache. For this option, the project must check in the
Pipfile.lock into the repository, and load both default and development packages into the cache.
See the example python-pipenv
project for an example of how this can be done.
Warnings
We recommend that you use the most recent version of all containers, and the most recent supported version of all package managers and languages. Using previous versions carries an increased security risk because unsupported versions may no longer benefit from active security reporting and backporting of security fixes.
Python projects
Extra care needs to be taken when using the PIP_EXTRA_INDEX_URL
environment variable due to a possible exploit documented by CVE-2018-20225:
An issue was discovered in pip (all versions) because it installs the version with the highest version number, even if the user had intended to obtain a private package from a private index. This only affects use of the
PIP_EXTRA_INDEX_URLoption, and exploitation requires that the package does not already exist in the public index (and thus the attacker can put the package there with an arbitrary version number).
Version number parsing
In some cases it’s not possible to determine if the version of a project dependency is in the affected range of a security advisory.
For example:
- The version is unknown.
- The version is invalid.
- Parsing the version or comparing it to the range fails.
- The version is a branch, like
dev-masteror1.5.x. - The compared versions are ambiguous. For example,
1.0.0-20241502can’t be compared to1.0.0-2because one version contains a timestamp while the other does not.
In these cases, the analyzer skips the dependency and outputs a message to the log.
The GitLab analyzers do not make assumptions as they could result in a false positive or false negative. For a discussion, see issue 442027.